On the vulnerability of palm vein recognition to spoofing attacks
Links
- PDF Attachments: 2015’On the vulnerability of palm vein recognition to spoofing attacks_Tome,Marcel_.pdf
- Zotero Links: Local library
Contributions and Important Conclusions
- The first evaulation of the vulnerability of palm vein recognition to spoofing attacks.
- This paper demonstrate that the printed images can easily attack the palmvein recognition system, and the approaches to improve the performance will also put more sever impact on the vulnerability of the systems.
Some Descriptions
- For these reasons, nowadays palm vein recognition technology is considered as a promising and trusted biometric.
- The fact that the vein pattern used for identification is embodied inside the palms prevents the data to be easily stolen, as opposed to face that can be captured with a camera or to fingerprints that can be collected from latent prints.
Motivation
motivation to use printed images:
- simple, without priori knowledge about the system
- it has been proved to be efficient in the context of other biometric, such as finger vein1, 2D face2 and iris3.
- This paper1 shown that the toner ink from the printer absorbs the Near Infra-Red (NIR) illumination
The vulnerability of finger vein system has been demonstrate in this paper1
Methods
- Local binary patterns (LBP) are applied as features
- The histogram intersection metric is adopted as a similarity measure to compute the scores
Experiments
The authors come from Idiap Research Institute, which released a python package for palm vein recognition, named
bob.palmvein, links herePaper code links here
Since the experimental details are not concerned, I only show some important results and conclusions.
- In normal case, the FAR of printed images is higher than 50%, which proves the vulnerability of the palm vein recognition system to spoofing attacks, establishing the necessity of securing them with an anti-spoofing method.
- Some approaches that can improve the performance (such as perprocessing, ROI alignment, increase the number of enrollment samples) would alse pose bad impact on the vulnerability of system.
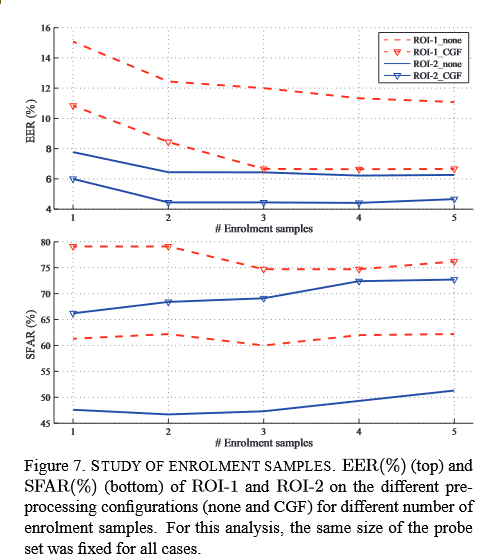 SFAR is the FAR of printed images.
SFAR is the FAR of printed images.
Inspiration
More technique are need to secure the system for anti-spoofing.
Maybe blood flow detection? Multiview (impossible in palm vein)? liveness detection.
Footnotes
-
P. Tome, M. Vanoni, and S. Marcel. On the vulnerability of finger vein recognition to spoofing. In IEEE International Conference of the Biometrics Special Interest Group (BIOSIG), volume 230, Sept. 2014. 2 ↩ ↩2 ↩3
-
I. Chingovska, A. Anjos, and S. Marcel. On the effectiveness of local binary patterns in face anti-spoofing. In Proceedings of the 11th International Conference of the Biometrics Special Interes Group, September 2012. 2 ↩
-
V. Ruiz-Albacete, P. Tome-Gonzalez, F. Alonso-Fernandez, J. Galbally, J. Fierrez, and J. Ortega-Garcia. Direct attacks using fake images in iris verification. In Proc. COST 2101 Workshop on Biometrics and Identity Management, BIOID, LNCS-5372, pages 181–190. Springer, May 2008. 2 ↩